Chris Spehn
@ConsciousHacker
Adversary Simulation @ IBM's X-Force Red.
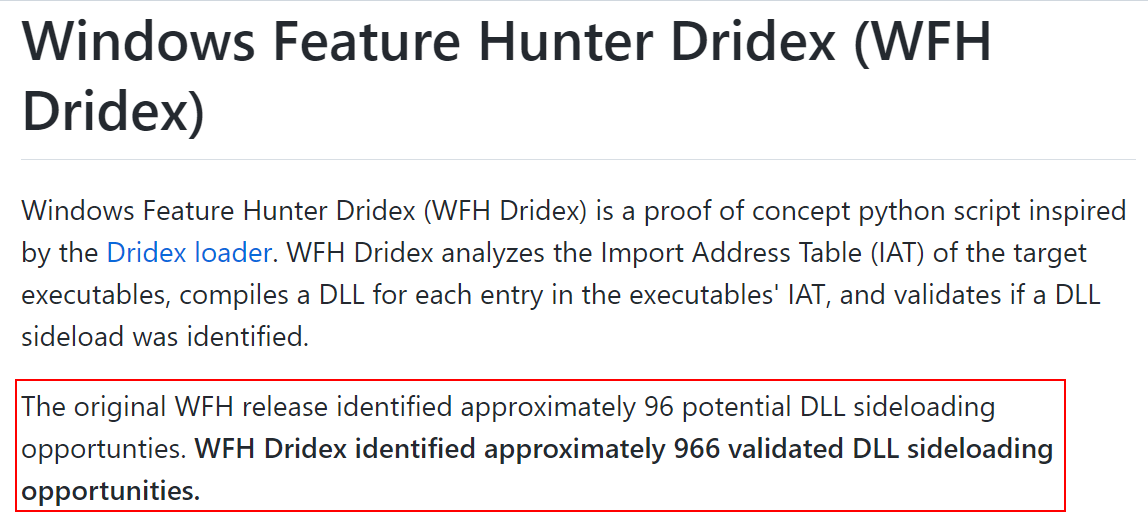
Today I'm releasing WFH Dridex, another approach to automatically identify and validate DLL sideloading opportunities inspired by the Dridex loader. I also submitted a pull request to @Wietze's HijackLibs project with 507 entries from C:\Windows\System32. github.com/ConsciousHacke…
I have three specific Vegas goals and they're all related to hats. We're going for the hat trick with @dreadnode, @SpecterOps, and @falconforceteam. Why? I'm a fan of these companies and their logos and I need new hats that I actually like.
We're heading to Vegas August 5-10! Send us a DM if you'd like to meet up onsite. Happy to share our latest offensive agents, AI red team tooling, custom evals, and training capabilities on the Strikes platform. Plus, "shiny rocks"??
My first @SpecterOps blog! Ever wanted to collect Active Directory information from LDAP for a Red Team? Using LDAP's more OPSEC-considerate cousin: ADWS can be used to improve upon the already present advantages of using smaller-scaling LDAP queries. specterops.io/blog/2025/07/2…
For those like me who prefer to stay in the terminal and want to call REST APIs like the Microsoft Graph without complicated commands or copy/pasting tokens: roadtx now has a graphrequest command to perform simple requests against these APIs and parse the JSON.
Hiring a junior/mid role on my team for a Red Team operator, feel free to DM me with any questions or anything nvidia.wd5.myworkdayjobs.com/NVIDIAExternal…
anyone else put on headphones and forget to turn on music for a few hours? just been sitting here listening to the soothing tones of tinnitus
We’re excited to have @RobertShala_XK, Co-Founder at @SentryCyber speaking at #BSidesTirana2025 on the 19th of September as part of a joint topic of discussion with Armend Gashi! #BSidesTirana #BSides #speakers 1/3
A short GitHub repository explaining on weaponizing WSL file extensions github.com/dmcxblue/WSL-P… #redteam
Extensions are problematic and they insert the attacker directly into sensitive contexts. The tradecraft shown is really weak (but it doesn't have to be), I think that illustrates there is a real issue here. Attacker ROI on the vscode store is high with multi-editor targeting.
But how could the infected developer, who was quite experienced, have downloaded this obviously malicious extension? It turns out that attackers have been able to make the malicious extension rank higher than the legitimate one. [3/6]
I’ll be at #blackhatusa25 with a group of the @MDSecLabs red team. If you want to meet up, grab a 🍺 or ☕️and talk c2s, OST or red teaming in general, drop us a line! ✅👋
Had some time and decided to take a shot at Fabian’s RAITrigger project. After a look into the RPC internals, I put together a super lightweight C# version (no NtApiDotNet), plus a C++ and BOF version. Enjoy! github.com/klezVirus/RAIW…
Excited! Come grab some stickers...the update includes a new "relay" module to support TAKEOVER-5. No more using a 2 year old pull-request that hasn't been merged yet.
Get to know what's new w/ SCCMHunter. Join @unsigned_sh0rt's #BHUSA Arsenal session on the post-exploitation tool & learn about the updates, including site system profiling, extended admin modules, & credential relaying capabilities. ghst.ly/3GkhpBV
Bypassing AMSI with your own custom COM interfaces inside CLR process - an excellent piece by Joshua Magri (@passthehashbrwn). The custom implementation allows to allocate and load assemblies from memory and invoke Load_2() method instead of typical call to Load_3(). This…
Uploaded mprecon, a tiny script I made while learning SCCM. It pulls info from MP server like DP locations, site version, build number, SMSID, and device's primary user etc. No special privileges are required. Sometimes works without authentication🤯 github.com/temp43487580/m…
Call For Speakers closes this Friday 7/18. Tell your friends. Tell your favorite offensive AI researchers. 🏃💨 sessionize.com/offensive-ai-c…
Great, now put the Open into OpenAI.
Plus users, the mic is yours. Record mode is now available to ChatGPT Plus users globally in the macOS desktop app.
SCCM’s Management Points can leak more than you’d expect. @unsigned_sh0rt shows how Network Access Accounts, Task Sequences, and Collection Settings can be stolen by relaying a remote Management Point to the site database. Check it out ⬇️ ghst.ly/4eNLaHU
Smb Signing is one of the best security measures an organization can take. Who has this fully enabled in their org?
We're learning!
About a year ago, @moo_hax and @monoxgas said we should reconsider the approach to offensive security in a private talk. At the time, while what they were doing was impressive, I dismissed the whole AI hype. Now here we are, fine tuning a model. Learning as much as we can.
PSA to anyone struggling, don't be told that "you're just worried", "you're just feeling sad", "you're overthinking things"... depression, anxiety, OCD, ADHD, Autism are killers. Talk, and advocate for yourself!
Finally landed on an OCD diagnosis yesterday, the fucking relief is unreal. Not like it's a shock, but it's been a loooooong time to get to this point. Look after your mental health h4xx0rz! youtube.com/watch?v=NDBRjB…